Easiest 2FA Bypass
Introduction
Hello there, everyone! And guess what? We’re in 2026 awesome, right? I hope you’re all doing great in your own timelines.
This blog is about a bug I found last month: the simplest 2FA bypass ever.
I wanted to share it now because I finally fixed my laptop and I’m back to writing a lot again.
Oh, and one more thing I updated my username from freyxfi to offsecrunner.
Maybe playing too much Cyberpunk has side effects on me lol.
Funny Story
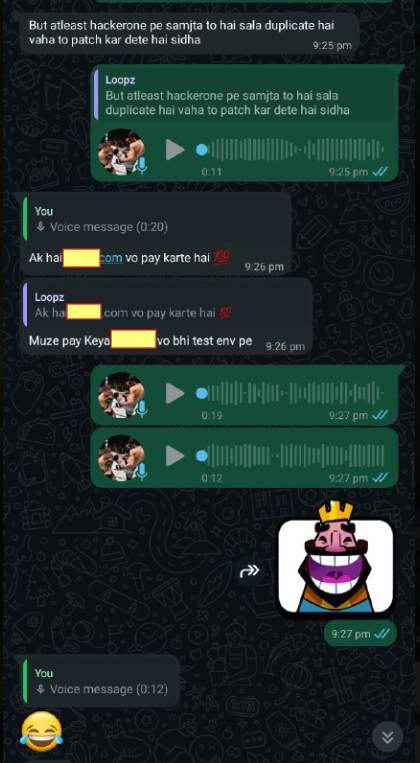
So, I have a friend named l00pz one of the most disciplined guys I’ve met.
This motherfucker wakes up at 5 AM every day which actually motivates me to get up early too. Lol
One day we were chatting about how AI is taking over everything (including HackerOne’s AI reviewing researchers’ reports).
We started talking about self-hosted programs and he shared one with me: boomboom.com.
He mentioned how little they paid him.
I had no real intention of testing it, but I clicked the link anyway and logged in.
As soon as I did instant vibe check: “Oh, now it’s all BAC and logic flaws here!”
So I logged out immediately.
Now the actual bug testing:
- I have a bad habit of jumping straight to user settings as soon as I enter any application.
- The only interesting thing I noticed was the 2FA option most small business sites don’t even offer it for free users.
- I activated 2FA.
- Went back to check if it was working correctly.
- Logged in again and connected my Google OAuth.
- Logged out.
- Logged in again using Google OAuth.
- Surprise 2FA completely bypassed!
I directly landed at:
https://eu1.target.com/sso/oauth?code=90d6e83f77c363f818cb14a22d24edefef1b47329c741b60f372bbe99c24&state=2b682de292c84062fb4e
…and I was already inside the app.
This was way too easy.
About a year ago I saw the exact same vulnerability on Glassdoor.
Let’s Understand Why This Happens (Because We Learn)
This isn’t rare it happens surprisingly often.
Here’s the breakdown:
- 2FA was enforced only on the password login flow, not on the OAuth login flow.
- You enable 2FA -> app sets
2FA_ENABLED = trueon your account (correct). - You log in with username + password → app enforces 2FA (good).
- You connect Google OAuth to the same account → link happens at account level, not per auth method.
You log out and log in via Google OAuth → backend treats Google’s verification as “strong enough” authentication → skips internal 2FA check completely.
- So when you hit: /sso/oauth?code=…&state=… The backend logic looks like this:
1
2
3
4
5
6
7
8
9
IF oauth_provider_verified == true
create session
skip 2FA
- Instead of the correct logic:
IF user.2fa_enabled == true
enforce 2FA
That’s the bug.
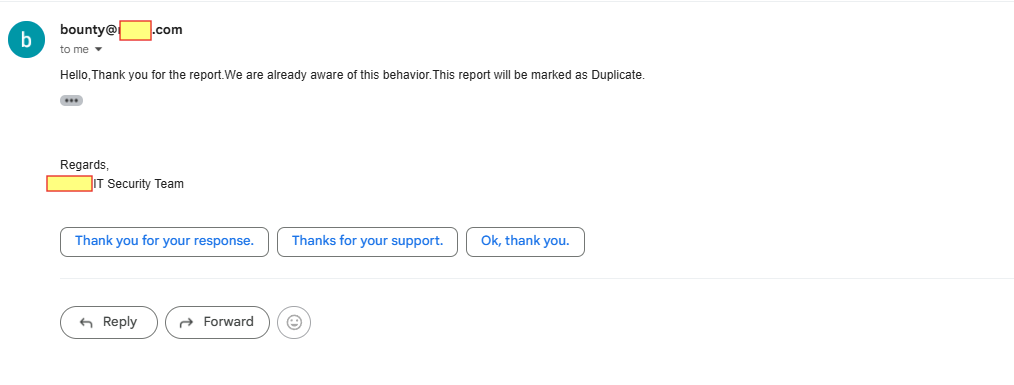
Response from the Team!
Now the team was like this
I would love to share the video PoC, but the issue still exists
Whats next?
Nowadays I am more focused on Red Teaming and getting a lot of hands on with Cobalt Strike and the war with EDRs! lol
So the next blogs will be more focused on that. I am going to make a habit of writing more cool stuff again.
BTW, if you use Discord and want to chat with me, please send a friend request: @offsecrunner this is my username.
And even if you are not from security and do MMA or something please invite me to spar :)
Until next time…..